LockMagic and Secure Workspace
Traditional Rights Management Systems needs all application that will integrate with it to be updated. In this system, if an RMS based application is outputs secure data, then another RMS based software will be needed to read and operate on that secure data.
If the applications that are being used are from third parties, then an organization needs to wait until all the apps from that third party is updated in order to use the intended data securely.
If there are many applications from many different third parties being used, then an organization needs to wait until all of the applications from all the third parties are updated before they can use them securely on the intended data. Further, there can be interoperability issues that prevent the different third party applications from working together. Lastly, if the applications are internal intranet application, then additional resources will need to be allocated to update all of the internal applications. If these internal applications produce data that will be consumed by third applications, then further testing between the internal and external applications needs to be done to ensure compatibility.
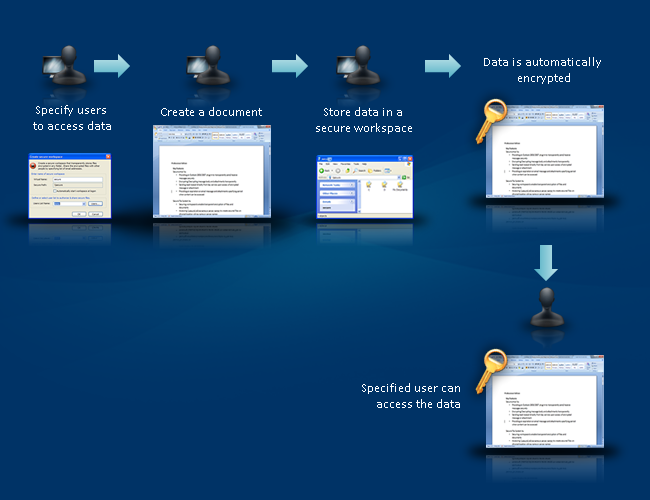
Using LockMagic’s Secure Workspace, these issues do not occur since the applications are not modified. The Secure Workspace intercepts all operating system calls and encrypts data before it is written to disk.
Highlights
- Seamlessly integrates into the Windows Operating System
- Compatible with Windows from XP to Win 10
- Applications remain unchanged
- Compatible with all applications
- Blocks untrusted applications from accessing encrypted data







